The Black Shadow: Exposing Iran's State-Sponsored Hackers
An investigation reveals the identities and Tehran offices of a state-linked cyber group targeting civilian infrastructure abroad.
A hacking group known as BlackShadow, operating as a cyber unit under Iran's Ministry of Intelligence (MOIS), has been publicly exposed following the release of new information identifying six additional members and multiple office locations in Tehran. The group, which uses the front company JahatPardaz IT Solutions, has been linked to a string of failed cyberattacks against Israeli civilian targets since 2020. Despite their ambitions to conduct sophisticated operations, the group's members have proven unable to conceal their own identities or the locations of their facilities, raising questions about the competence of state-backed hacking units and the consequences for ordinary Iranians.
BlackShadow first emerged in 2020 as a threat actor targeting Israeli entities. Their stated objectives included disrupting civilian infrastructure, stealing sensitive data, and fomenting social unrest. However, subsequent investigations revealed that the group was not an independent hacker collective but a dedicated cyber unit operating under the direct command of Iran's Ministry of Intelligence. The group operates through a front company registered in Tehran called JahatPardaz IT Solutions. This commercial facade provides the hackers with office space, salaries, and the appearance of legitimacy while they conduct their operations. Intelligence agencies have previously noted that BlackShadow maintains close operational ties with Hezbollah's cyber unit and other proxy forces supported by Tehran. The group is also known by multiple aliases in the cybersecurity community, including Agrius, Deadwood, SharpBoys, and DEV-0022, suggesting efforts to mask their identity through brand proliferation.
Despite these attempts at concealment, the group's operational security has been consistently poor. Their offices have been relocated multiple times, yet each new location has been identified and publicly disclosed. The most recently exposed address is located on Motahari Street in central Tehran, at the intersection of Soleiman Khater Alley and Aslipour Lane. Previous facilities included a building on Noor Mohammadi Street off Shariati Street, and another on Qanbarzadeh Alley near Eshgh'yar Street in the Soleimani Highway area.
New information has revealed the identities of six individuals associated with the BlackShadow cyber unit. These men are believed to be operators working out of the group's Tehran facilities, conducting attacks against foreign targets from their keyboards while based in the Iranian capital.
The identified members are:
Photo | Full Name |
|---|---|
 | Meysam Nosrati Azar |
 | Seyed Hossein Mousavi Khoshdel |
 | Seyed Mojtaba Razavi Keneti |
 | Mohsen Soleimani |
 | Hamid Tavassolian |
 | Amirhossein Bagheri |
 | Alireza Rahimi Astane |
 | Mohammad Ariyan |
 | Ali Geranmaye |
 | Arash Khodabande |
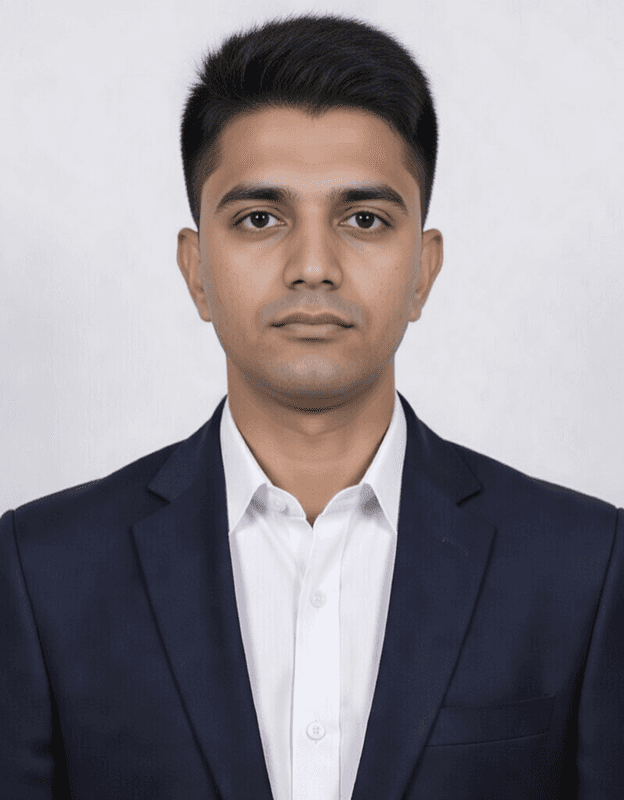 | Mohammad Sajjad Shohrabi |
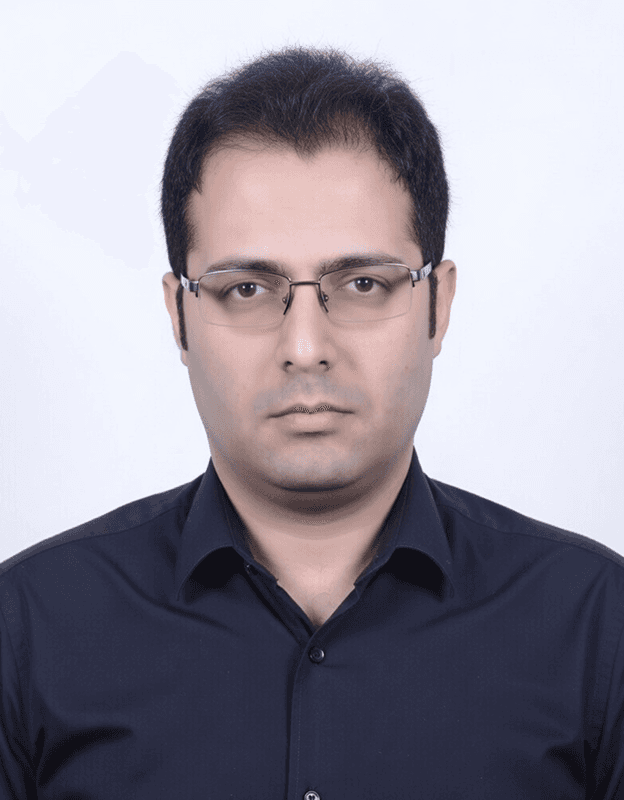 | Amir Hossein Madani |
 | Hossein Arzani |
 | Javad Jahdi Kanzegh |
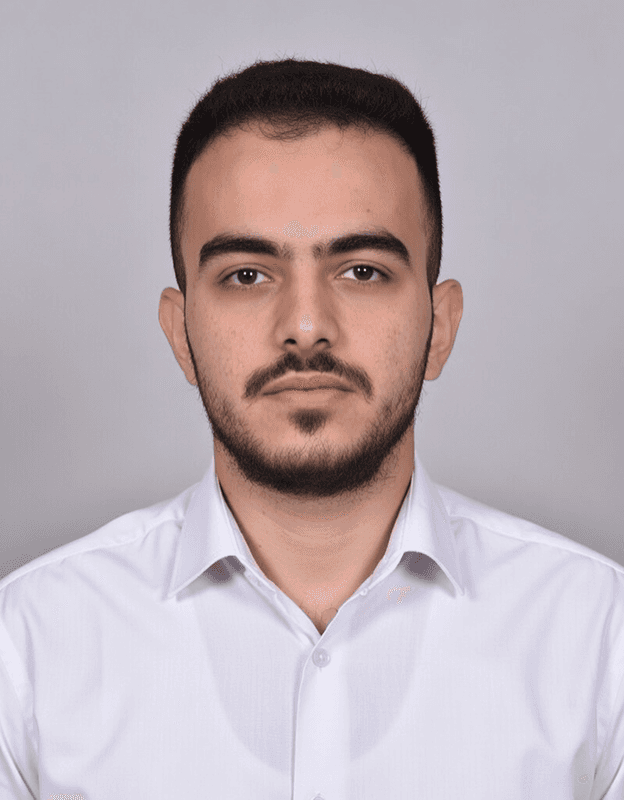 | Mohammad Moeinian |
These names add to a growing list of previously exposed operatives linked to the group. Additionally, an individual identified only as "Mohsen" has been observed visiting their offices, though his precise role within the organization remains unclear. The repeated exposure of personnel suggests either significant internal leaks or systematic monitoring by actors opposed to the group's activities.
The group's self-image stands in stark contrast to their actual track record. They project an image of themselves as a formidable cyber organization capable of inflicting serious damage on adversaries. In practice, however, every significant attack they have attempted in recent months has been detected and neutralized before causing substantial harm.
BlackShadow's operational methods rely heavily on phishing attacks designed to compromise email accounts and gain access to sensitive systems. Their targeting has focused primarily on Israeli civilian infrastructure, including hospitals, shipping companies, and insurance firms. These attacks are intended to steal information, disrupt services, and create panic among civilian populations.
However, the group's effectiveness appears to be minimal. According to cybersecurity analysts tracking their activities, each new phishing campaign launched in recent weeks has been identified and thwarted at an early stage. Their infrastructure is routinely burned, their malware detected, and their command-and-control servers exposed before they can achieve their objectives.
The irony of their situation is difficult to overstate. They claim to be an invisible force capable of striking from the shadows, yet they cannot even protect their own members from being identified on the streets of Tehran. They have lost the ability to credibly deny their ties to the Ministry of Intelligence, as their front companies and office locations have been documented and publicized repeatedly.
The repeated exposure of BlackShadow's members and facilities reveals a pattern of operational incompetence combined with institutional impunity. The group's operators continue their activities despite being publicly named, suggesting they face no consequences for their failures and no risk of prosecution. They operate openly in Tehran's neighborhoods, relocating only when their addresses become too hot to ignore.
This impunity extends to the institutional level. The Ministry of Intelligence, which oversees and directs the group's activities, has never been held accountable for running a cyber unit that targets civilian infrastructure in violation of international norms. The front companies continue to operate, the salaries continue to be paid, and the hackers continue their attempts to penetrate foreign systems despite their consistent failure.
For ordinary Iranians, however, the consequences are tangible. Each exposed operation brings financial burden and reputational damage to the country on the global stage. The actions of groups like BlackShadow contribute to international sanctions, diplomatic isolation, and the perception of Iran as a state sponsor of destabilizing cyber activities. The hackers themselves remain insulated from these consequences, sitting comfortably in their Tehran offices while their compatriots bear the costs.
The BlackShadow case reveals deeper truths about the structure of state-backed cyber operations. The group embodies a paradox: they are at once an arm of an intelligence agency and a collection of individuals whose personal identities have become public knowledge. Their repeated exposure demonstrates that operational security is not merely a technical challenge but a fundamental weakness that state actors struggle to overcome.
The group's continued existence despite their track record of failure suggests that their function may be as much about signaling capability as about achieving concrete results. For the Ministry of Intelligence, maintaining a cyber unit that periodically launches attacks, even unsuccessful ones, demonstrates continued commitment to asymmetric warfare. For the operators themselves, the positions provide stable employment and a sense of participation in national projects.
Yet the cumulative effect of these exposures is to undermine the very mystique that groups like BlackShadow depend upon. They chose their name to evoke invisibility and menace, but the reality revealed by investigative work is one of mundane offices, exposed personnel, and failed operations. The shadow, it turns out, is not nearly as dark or as large as they would like the world to believe.