The Cyber Academy: Inside the Islamic Republic’s Secret School for Hackers
An investigation exposes a state-linked academy recruiting and training hackers for global cyberattacks and domestic repression.

Operating from an unassuming office in central Tehran, an organization officially registered as a non-commercial institute for “cybersecurity education” functions as a clandestine recruitment hub and operational front for the Islamic Republic’s most aggressive state-sponsored hackers. Known as the RAVIN Academy, this entity has been sanctioned by the United States, the European Union, and the United Kingdom for its role in cyber-enabled repression. This investigation reveals the identities and roles of key figures behind the academy, detailing how they leverage public-facing “technology olympiads” and university partnerships to scout and groom young Iranian tech talent. These recruits are funneled into a coordinated ecosystem of hacking groups that carry out disruptive attacks against foreign governments and critical infrastructure while aiding the regime’s domestic surveillance and crackdowns. The RAVIN Academy exemplifies the institutionalization of state cyber power, blending education, commercial cover, and military intelligence objectives.
The RAVIN Academy was formally registered in early 2020 as the “Ravin Smart Voice” non-commercial institute. Its founders were two young members of the Ministry of Intelligence, establishing from the outset a direct link to the state’s security apparatus. The academy’s stated mission is cybersecurity training, a legitimate-sounding cover that provides both a recruitment pool and a veneer of professionalism.
Its physical headquarters is located at 105 Solaiman Khater Street, off Motahari Street, in the heart of Tehran. Internally, the organization is structured with a board of directors, instructors, and employees. Investigations into its corporate filings and operational patterns identify at least 16 core members who manage its activities, which include talent scouting, providing logistical and financial support to hacking groups, and laundering the origins of their operations.
The academy’s public-facing activities are strategically designed to blend into Iran’s tech landscape. A key initiative is its involvement in a national “Technology Olympics,” an event co-organized by the Iranian Vice Presidency for Science and Technology and the Pardis Technology Park. These competitions, featuring cyber attack and defense challenges, serve as a perfect screening ground to identify skilled individuals unaware they are being assessed for recruitment by state security organs.
The leadership and key personnel of the RAVIN Academy are not shadowy anonymous figures but individuals with documented careers whose ties to the state have been progressively exposed. Internal investigations have identified the following key individuals central to the academy's operations:
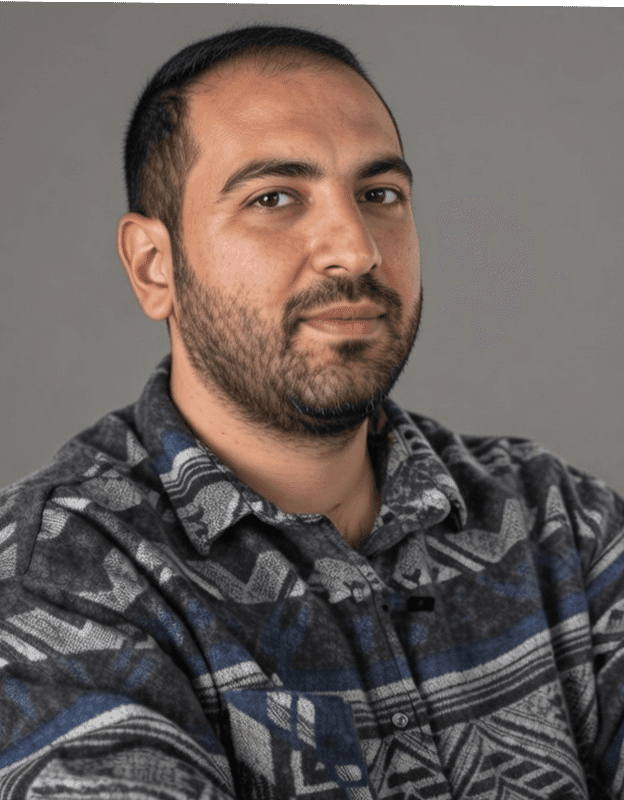
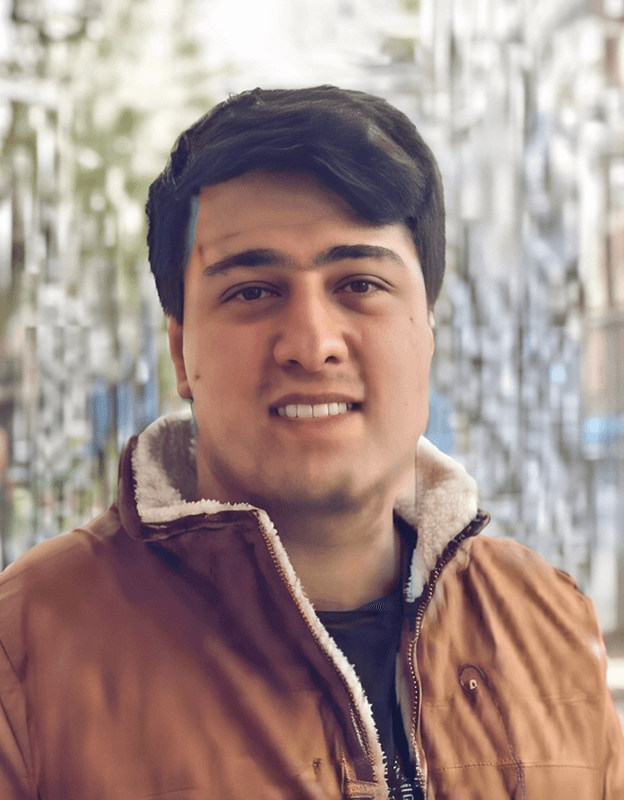
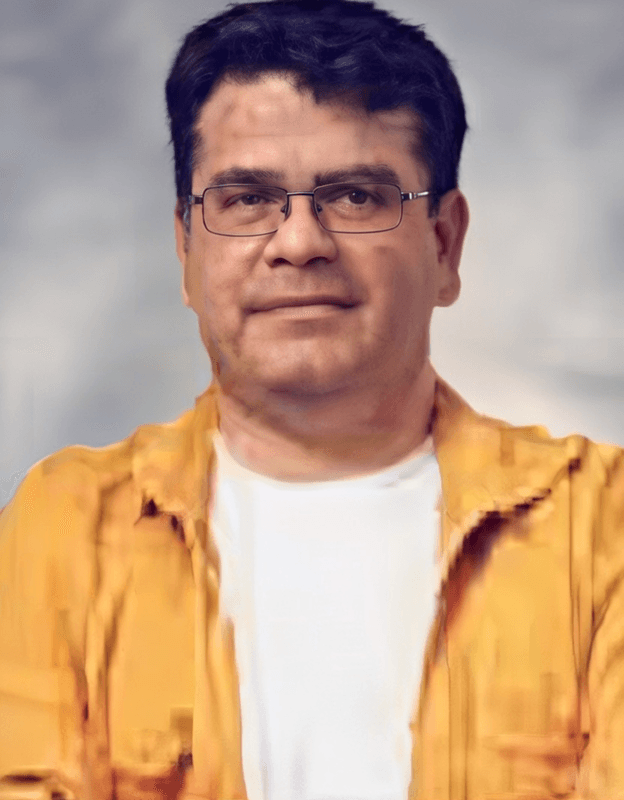
Photo | Full Name | Role in RAVIN Academy |
|---|---|---|
 | Mojtaba Mostafavi | CEO & Co-Founder |
 | Farzin Karimi | Co-Founder & Instructor |
 | Hamed Soltanpour | Instructor / Member |
 | Reza Sharifzadeh | Instructor / Membe |
 | Ahmad Hosein Halvaei | Instructor / Member |
 | Hosein Siyahpoush | Board Member, Leader of DarkBit hacking group |
 | Mohammad Siyahpoush | Instructor / Member |
 | Mohammad Hasan Doroodian | Instructor / Member |
 | Mohammadreza Teymoori | Instructor / Member |
 | Mohammad Hatami | Instructor / Member |
 | Mehdi Mirsoltani | Instructor / Member |
 | Ramin Farajpour | Instructor / Member |
 | Borna Nematzadeh | Instructor / Member |
 | Ali Tabatabaei | Instructor / Member |
 | Amin Dadashi | Instructor / Member |
These individuals, born in the late 1980s and early 1990s, represent a new generation of intelligence officers: tech-savvy, comfortable in corporate and academic settings, and operating under their real names until international sanctions publicly identified them as formal officers of the Ministry of Intelligence.
The RAVIN Academy’s methodology is a multi-stage process of identification, cultivation, and deployment. The initial contact is often made through legitimate-seeming channels like public competitions or university workshops. Promising individuals are then drawn into the academy’s training programs, which blend genuine technical instruction with ideological alignment and operational tasking.
The academy does not act alone but serves as a management hub and talent pipeline for affiliated hacking groups. These groups, including DarkBit, conduct offensive cyber operations aligned with the Islamic Republic’s strategic interests. Documented targets, according to sanctions designations and investigative reports, include:
Government systems in Italy, Algeria, Jordan, Turkey, Saudi Arabia, Iraq, and Pakistan.
Critical infrastructure, most notably the Aramco oil facilities.
Academic and municipal institutions in Israel.
Domestically, the academy and its network played a documented role during the nationwide protests that began in 2022. Hacking groups associated with the state were utilized to identify protesters, facilitating their arrest and persecution. This dual-use capability, projecting power abroad and enabling repression at home, is central to its value to the regime.
The entire operation enjoys high-level political patronage. The Supreme Leader, Ali Khamenei, has publicly expressed a personal fascination with the cyber domain, once remarking that if he were not the leader, he would wish to head the Supreme Council of Cyberspace. This signal from the top legitimizes and prioritizes the development of offensive cyber capabilities as a core pillar of state power.
The RAVIN Academy operates with a significant degree of impunity, protected by its state sponsorship and the diffuse, deniable nature of cyber operations. While international sanctions have named and targeted the institution and its leaders, they remain active within Iran, continuing their recruitment and operations. The use of corporate structures and educational fronts provides legal and administrative cover within the country.
The academy’s existence is not an aberration but a symptom of deep systemic integration. It represents the formalization of “cyber militias” directly tied to the Ministry of Intelligence. The involvement of figures from the national internet censorship apparatus (like Aradavan) underscores the regime’s holistic view of the digital space: a domain to be controlled internally and weaponized externally.
The consequences are twofold. For the international community, it presents a persistent threat from a resilient network capable of attacking critical infrastructure and conducting espionage. For Iranian society, particularly its youth and tech sector, it represents a predatory co-option of talent. Young programmers and engineers are lured with the promise of technical challenge and career growth, only to be inducted into a system that uses their skills for repression and cyber warfare, jeopardizing their futures and exposing them to international sanctions.
The RAVIN Academy model reveals a strategic adaptation. Facing skilled brain drain and international isolation, the regime has built a self-sustaining, state-funded ecosystem to cultivate and weaponize its remaining technical talent. It is a clear investment in asymmetric warfare, where a small group of hackers can project power and sow chaos disproportionate to their numbers, all while the state maintains a thin but persistent layer of plausible deniability. This institutionalization marks a mature and dangerous phase in the Islamic Republic’s use of cyberspace as an extension of its security doctrine.